SecurityAdvisoryCouncil.com
Security Risk Analysis - Issues - Strategies - Solutions - Resources
Security Risk Advisory Consultants - Security Planning & Education
Security MostWanted For America!
Threat Intelligence
By Signing Up For Our News Letter, You Will Receive The Latest Security News
Once-A-Month!

Threat Intelligence Overview
Threat intelligence is the evidence-based knowledge and context about existing or emerging security threats that is analyzed and used to inform decisions, enabling organizations to move from a reactive to a proactive security posture. It goes beyond raw data by providing insights into the "who, what, when, where, why, and how" behind cyber threats.
Key Components
Threat Data vs. Threat Intelligence: Raw threat data (e.g., a list of suspicious IP addresses or file hashes) only becomes "intelligence" after it has been processed, analyzed, and given context relevant to an organization's specific environment and risks.
Actionable Insights: The primary goal is to provide information that security teams and business leaders can act upon to prevent or mitigate attacks, allocate resources effectively, and manage risk.
Adversary Focus: Threat intelligence focuses on understanding the threat actors, their motivations (financial gain, espionage, etc.), and their tactics, techniques, and procedures (TTPs) to anticipate future attacks.
Types of Threat Intelligence
Threat intelligence is generally broken down into several types to serve different audiences and purposes within an organization:
Strategic Intelligence: High-level, non-technical information about the overall threat landscape, emerging trends, and geopolitical factors. This is for executives and decision-makers to guide long-term security strategies and investments.
Operational Intelligence: Detailed insights into specific upcoming campaigns or the methods of particular threat actors.
It helps security teams understand the context of potential attacks and plan defense mechanisms.
Tactical Intelligence: Technical data and specific indicators of compromise (IoCs), such as malicious IP addresses, domain names, and file hashes. This is used by front-line security operations center (SOC) analysts for immediate detection and response.
Technical Intelligence: In-depth technical analysis of malware, exploits, and vulnerabilities to help specialized teams develop specific detection and remediation tools.
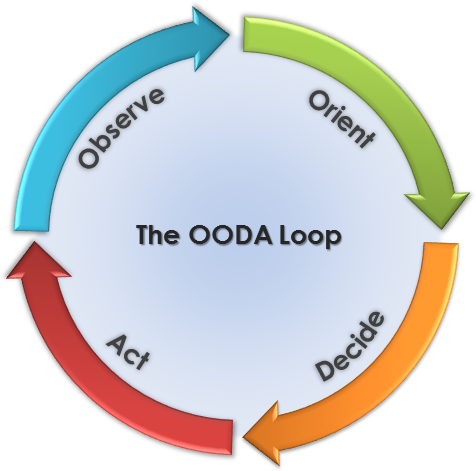
The Threat Intelligence Lifecycle
The creation and application of threat intelligence is a continuous, cyclical process:
Direction/Planning: Define the specific goals and requirements for the intelligence program based on organizational needs and assets.
Collection: Gather raw data from various sources, including internal logs, open-source intelligence (OSINT), commercial feeds, and the deep/dark web.
Processing: Refine and normalize the raw data into a usable format, filtering out noise and irrelevant information.
Analysis: Analyze the processed data to identify patterns, trends, and connections, turning it into actionable intelligence that meets the initial requirements.
Dissemination: Share the finished intelligence with the appropriate stakeholders in an understandable format tailored to their roles (e.g., a high-level report for executives or specific IoCs for analysts).
Feedback: Gather feedback from the intelligence consumers to evaluate its effectiveness and refine the requirements for the next cycle, ensuring continuous improvement.
Benefits
Implementing a robust threat intelligence program helps organizations to:
Shift from a reactive to a proactive security stance.
Make better-informed decisions about security investments and risk management.
Improve incident response times and reduce the impact of successful breaches.
Prioritize vulnerability patching efforts based on real-world threat data.
Enhance the overall security posture and build resilience against evolving threats.
Latest Trends in Threat Intelligence
The latest trends in threat intelligence (CTI) are largely driven by the adoption of Artificial Intelligence (AI) by both defenders and attackers, the rise of identity-based attacks using stolen credentials, and increased focus on critical infrastructure and supply chains as key targets.
Key Trends in Threat Intelligence
AI as a Double-Edged Sword: Both defenders and threat actors are using AI.
For Defense: AI and Machine Learning (ML) are being integrated into security operations centers (SOCs) to automate data analysis, prioritize alerts, and accelerate incident response, moving security from reactive to proactive threat hunting.
For Attack: Adversaries use generative AI to create highly personalized and convincing phishing emails, develop evasive polymorphic malware, and leverage deepfakes for sophisticated social engineering and fraud.
Rise of Identity-Based Attacks: The use of valid but compromised accounts is a dominant initial access vector.
Infostealer Malware: There has been a significant increase in info-stealing malware delivered via phishing, with a thriving "access-as-a-service" market on the dark web selling stolen credentials.
Targeting Centralized Authority: Attackers are focusing on cloud-based single sign-on (SSO) portals to gain broad access across an organization's systems.
Focus on Critical Infrastructure and Supply Chains: Geopolitical tensions are fueling state-sponsored activities that target critical sectors like energy, manufacturing, and telecommunications to pre-position for potential future disruption.
Ransomware Evolution and Diversification: While ransomware incidents have seen a slight decline overall, the attacks are becoming more sophisticated, often employing multiple extortion tactics (encrypting data and threatening to leak it). The Ransomware-as-a-Service (RaaS) model continues to lower the barrier for entry for less skilled criminals.
Proactive Threat Hunting and Predictive Analytics: Organizations are shifting towards proactive security measures, using predictive analytics and knowledge graphs to anticipate potential attack vectors and identify vulnerabilities before they are exploited.
Increased Collaboration and Information Sharing: There is a growing recognition of the need for public and private sectors to share threat intelligence to build collective resilience against common adversaries.
These trends highlight a cyber landscape where speed, automation, and a deep understanding of adversary motivations are crucial for effective defense.
Threat Intelligence Sources
Here are links to widely used and authoritative threat intelligence sources, feeds, and resources:
Authoritative & Government Sources
CISA Automated Indicator Sharing (AIS): A free, machine-readable service from the U.S. Cybersecurity and Infrastructure Security Agency for exchanging cyber threat indicators.
CISA Known Exploited Vulnerabilities (KEV) Catalog: An authoritative list of vulnerabilities confirmed to be exploited in the wild, crucial for patch prioritization.
MITRE ATT&CK®: A globally accessible knowledge base of adversary tactics and techniques based on real-world observations.
Free & Open-Source Feeds
SANS Internet Storm Center (ISC): Provides a free threat intel feed, analysis, and step-by-step mitigation instructions from a large sensor network.
LevelBlue Labs Open Threat Exchange (OTX): A large, community-led network for sharing Indicators of Compromise (IoCs) and threat intelligence.
Spamhaus: Offers blocklists for email security, focusing on IP addresses and domains used for spam and malware.
abuse.ch URLhaus: A community effort to share malicious URLs and domains used for malware distribution and phishing.
OpenPhish: Provides intelligence on active phishing threats with both free and premium options.
GreyNoise: Curates intelligence on internet-wide scanners and background noise to help security teams focus on relevant threats.
Comprehensive Threat Intelligence Platforms & Tools
Cisco Talos Intelligence Group: One of the largest commercial threat intelligence teams, offering comprehensive threat intelligence research and analysis.
MISP (Malware Information Sharing Platform): An open-source software platform for sharing, storing, and correlating threat intelligence.
VirusTotal: A free service that analyzes suspicious files and URLs to detect types of malware and share them with the security community.
Recorded Future: A major intelligence company offering comprehensive coverage across adversaries, infrastructure, and targets.
GitHub Awesome Threat Intelligence resources: Curated lists of various tools, sources, and frameworks for threat intelligence professionals.
Other Cybersecurity Communities & Forums
In addition to general sources, there are numerous other communities and forums where cybersecurity professionals share threat intelligence, ranging from professional organizations to active online discussion boards and instant messaging platforms.
Professional Organizations & Information Sharing
These organizations often have private, vetted communities for members to share sensitive or high-level intelligence.
InfraGard: A public-private intelligence-sharing program coordinated by the FBI to strengthen the security of U.S. critical infrastructure.
Information Security Forum (ISF): A global, independent organization that provides frameworks, research, and guidance for managing information security risks, with a strong internal community for members.
Cyber Threat Alliance (CTA): An organization where top cybersecurity companies share threat intelligence to improve defenses across the industry.
International Association of Cyber Threat Intelligence Analysts (IATIA): A professional organization dedicated to advancing the field of CTI and connecting analysts worldwide.
ISACA Engage: The online community platform for ISACA members, where thousands of professionals discuss best practices, certifications, emerging tech, and threat trends
General Cybersecurity Forums & Communities
These public forums are great for staying updated on the latest news, asking questions, and networking with peers.
Reddit: Various subreddits are active hubs for CTI and security news, including:
Bleeping Computer: A widely visited site with an active forum where users and experts discuss the latest security threats, malware removal, and technology news.
Dark Reading & Threatpost: Well-known news sites featuring articles and expert opinions, with comment sections and communities that serve as a source of shared knowledge.
Wilders Security Forums: A long-standing community for discussions on online privacy, security software, and data protection.
Real-Time Sharing (Discord & Slack)
For real-time collaboration and quick information sharing, Discord servers are increasingly popular.
Core CTI Discord: A community focused on the collaborative development and discussion of actionable CTI.
ThreatHunter Community Discord: A dedicated space for threat hunting discussions and sharing information.
BlueTeamVillage Discord: A community for defenders to share knowledge, resources, and best practices.
OSINT Curious & Project Owl: Communities focused on open-source intelligence gathering and methodology.
On this page you will find a wide variety of links to some of the most Threat Intelligence resources you have ever seen. I don't believe there is another website that presents such informed and in some cases classified internet resources that we reveal here. We sincerely hope you find information and the intelligence you seek to safeguard you, your business, and your organization or agency from harm.
Thank You for being here and being concerned with what is happening in our world today.
Take care and be aware!
JW Davis
President & CEO
SecurityAdvisoryCouncil.com
Email: admin@SecurityAdvisoryCouncil.com